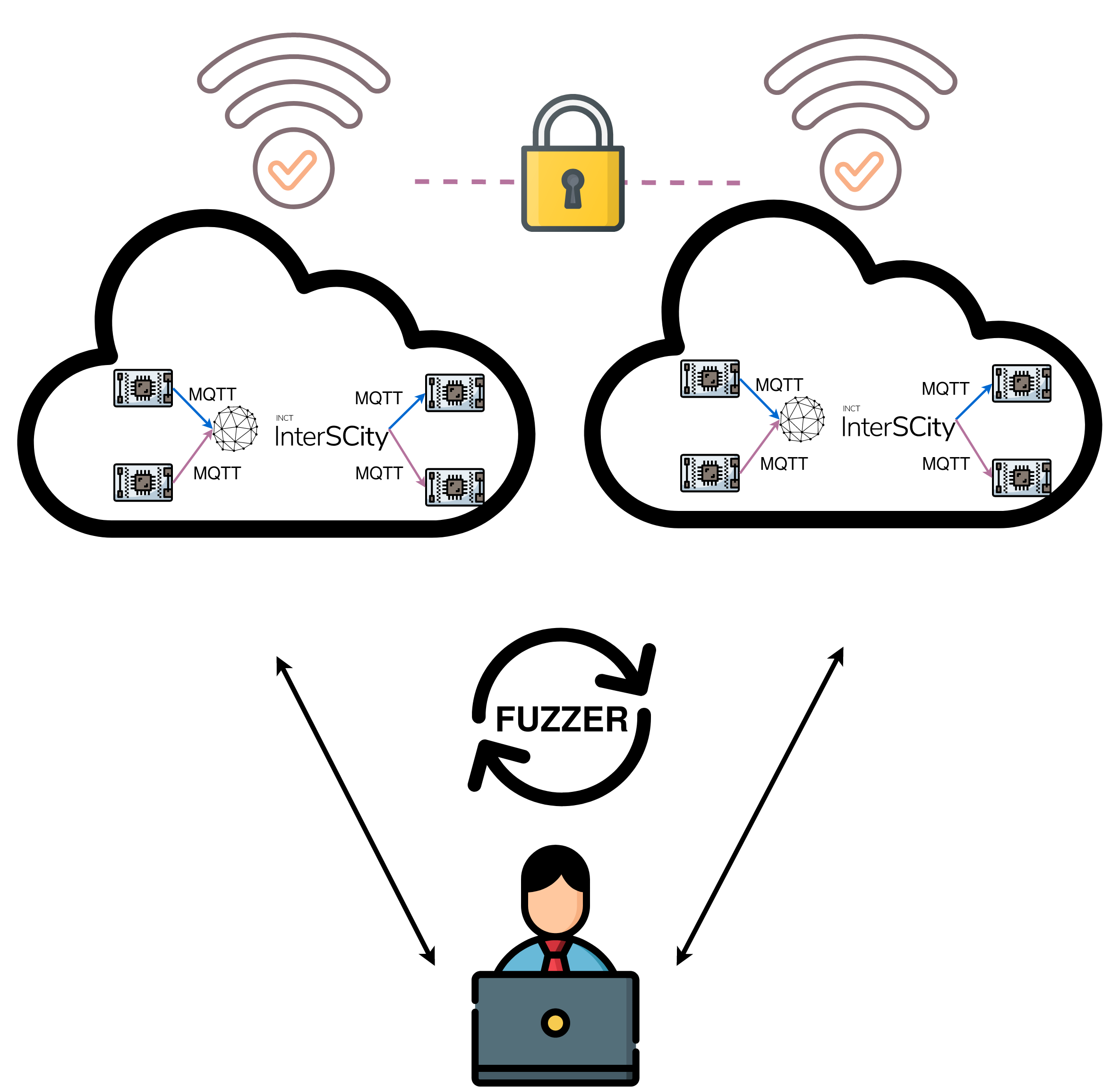
IoT implementations are vulnerable mainly because developers place more emphasis on functionality rather than security. In fact, smart city initiatives are usually deployed without security testing. For instance, MQTT protocol, the most widely-used IoT protocol, has been implemented for several uses, including medical equipment, airplane coordination, and home automation systems, but it was not designed with security in mind. Security-by-design, preventive, and proactive approaches are needed to mitigate potential threats; identify possible attack scenarios; reduce economic losses; and minimize complex patches in IoT environments. This research theme proposes four mechanisms to evaluate and improve security in IoT: an open source testing tool based on fuzzing, in order to analyze and minimize design issues in the MQTT protocol; a methodology to improve security updates; an authenticated cryptographic key agreement protocol; and the deployment of MQTT in two testbeds with the integration of the protocol in the InterSCity platform.
Icons made and authorized to use by iconixar
Coordinator:
Prof. Daniel Macedo Batista, IME-USP
Other researchers:
Prof. Dr Routo Terada, IME-USP
Prof. Dr. Arlindo Flavio da Conceição, IME-USP
Dr. Higor Amario de Souza, IME-USP
Students:
Luis Gustavo Araujo Rodriguez, IME-USP
Poliana de Moraes, IME-USP
External collaborator:
Prof. Guofei Gu, Texas A&M University